Standard CVE detection across your dependency tree. npm, pip, maven, gems, Go modules, cargo.
Traditional SCA flags every CVE in your dependency tree. We trace execution paths to find the ones that actually reach production.
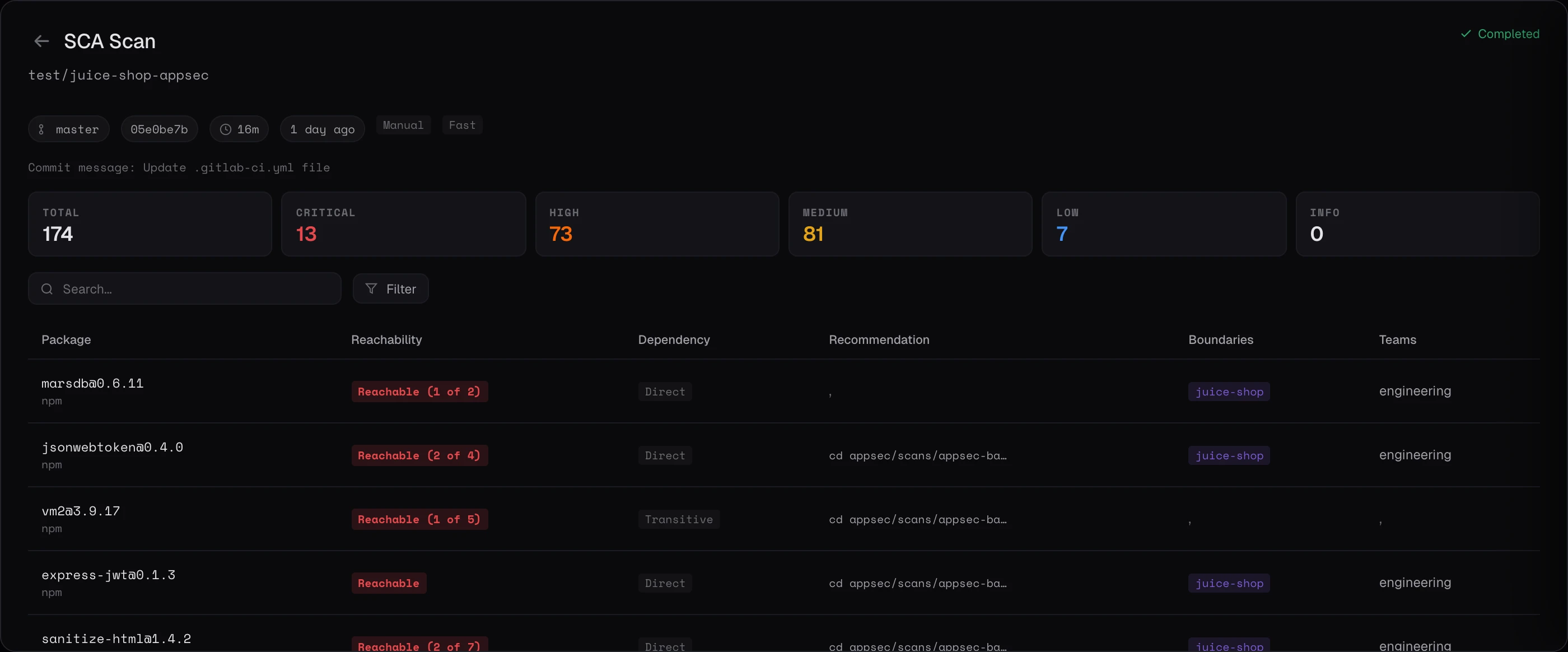
A typical SCA scan flags hundreds of CVEs. Most never execute. A research agent pinpoints each vulnerable function. The Code Property Graph checks whether your code calls it. Execution tracing confirms whether the call path is ever reached. The rest is noise.
Legacy SCA stops at the lockfile. It tells you a vulnerable library is present, but not whether the vulnerable code ever runs. Three checks get skipped.
An advisory typically flags a specific method signature, not the whole package. The actually-vulnerable surface is a small subset of what ships in the library.
Many libraries ship with APIs you never touch. A package can carry a critical CVE in a module your code never imports, and a lockfile scan cannot tell the difference between a real call site and an unused export.
Even if you call it, dead code, conditional compilation, and test-only paths often keep it from ever running in production. Reachability requires walking the path from a live entry point, not just confirming a syntactic reference.
Pinpointing the vulnerable function, confirming a real call site, and proving runtime reachability collapses the long tail of lockfile CVEs into a short list your team can actually fix.
See how reachability works ↓Five stages, from dependency scan to prioritized verdict. Static CVE lists in, proven executable paths out.
Standard CVE detection across your dependency tree. npm, pip, maven, gems, Go modules, cargo.
A research agent reads each advisory and extracts the exact vulnerable function or method signature, not just the package version.
Keygraph queries the Code Property Graph to check whether your code imports and calls the specific vulnerable function.
We walk forward from application entry points to confirm whether the vulnerable code is actually reachable at runtime.
Proven Executable, Likely Reachable, or Not Reachable. Triage by impact, not lockfile presence.
Not every vulnerable dependency is exploitable. Reachability Analysis tells you which ones matter.
For function-level vulnerabilities. Keygraph runs data-flow analysis to trace execution paths from your code into the vulnerable dependency function. The report shows total paths analyzed, confirmed reachable paths, and unvalidated paths. Each finding includes specific sink locations (file, line, code snippet).
For library and framework vulnerabilities where code-level data flow isn't applicable. Analyzes how the vulnerable package is imported and used across the codebase. Distinguishes production usage from test-only usage, evaluates exposure conditions and mitigating factors.
NOT_REACHABLE downgrades risk to Low regardless of CVE severity. CONFIRMED_REACHABLE plus a High CVE elevates to Critical. POTENTIALLY_EXPOSED plus a Medium caps at Medium. Developers see the risk that matters, not just the CVE score.
Schedule a demo and watch reachability-aware SCA run against your dependency tree.