Confirmed findings come back as reviewable pull requests: internally verified, ready for your developers to approve.
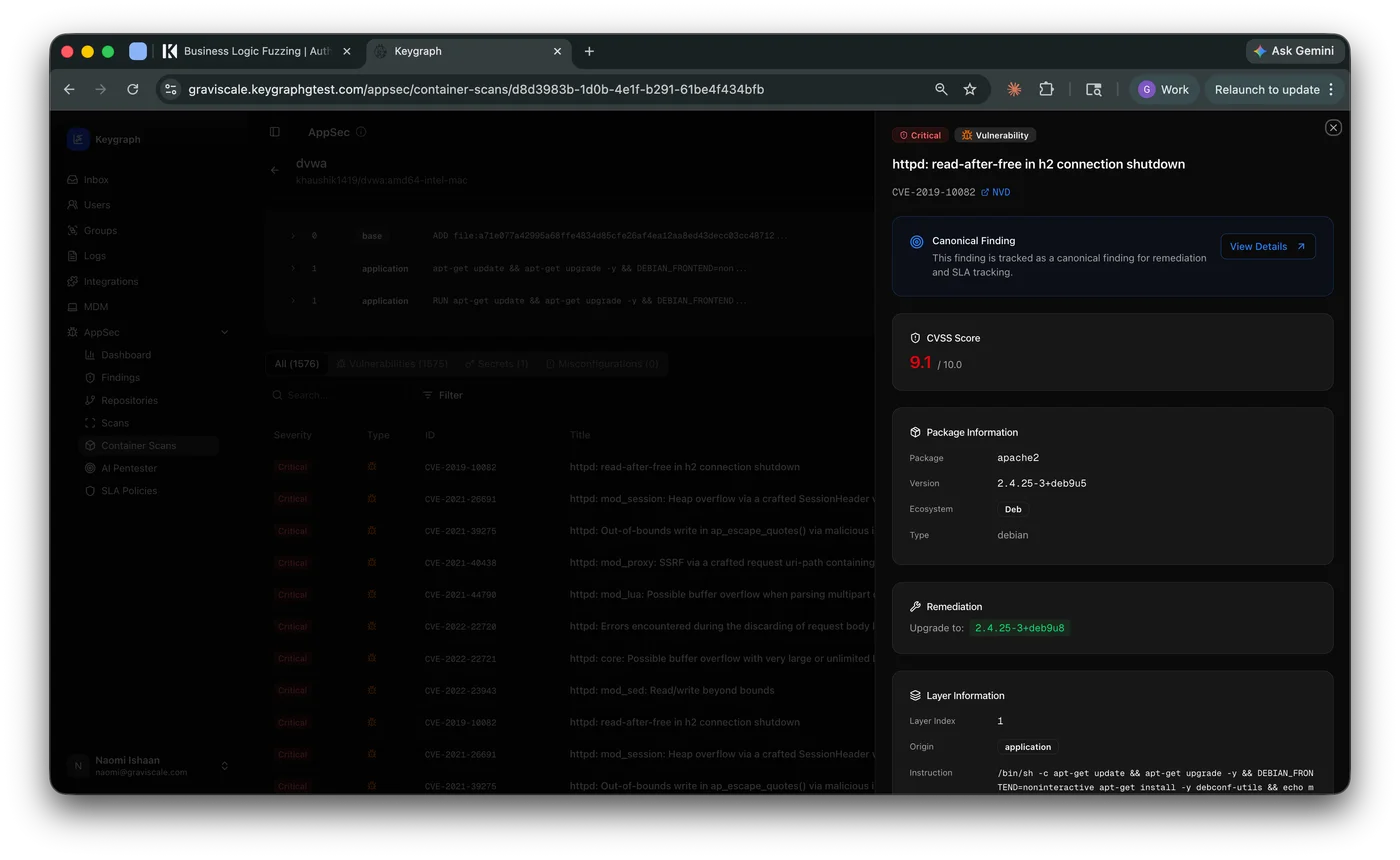
From finding to reviewable PR, autonomously. Click a finding in Keygraph. An agent reads the evidence, writes the fix, runs it past the original scanner to prove the vulnerability is gone, and opens a draft pull request under a Keygraph bot identity. Your developers review and merge, just like any other change.
Code Remediation operates on the scan types where an automated patch is honest and high-confidence, and lands in the source control your team already uses.
Point issues, data-flow vulnerabilities, and confirmed business-logic findings.
Misconfigurations and policy violations across Terraform, Kubernetes manifests, Dockerfiles, and CI workflows.
Confirmed exploits from the agentic pentester come back as patches with the exploit record attached as evidence.
SCA, Secrets, and Container remediation are on the roadmap.
Source control coveragePatches open as draft PRs in your existing GitHub Cloud or GitHub Enterprise Cloud organization. Self-hosted GHES support is on the roadmap.
All GitLab hosting modes are supported, including GitLab Self-Managed (CE and EE) at modern versions. Patches arrive as merge requests in the same project.
Before a pull request is ever opened, the patch has to prove it closed the original vulnerability. If it doesn't, no PR. No noise in your queue.
Keygraph re-runs the same scanner that produced the finding against the patched code, scoped to the affected files. The vulnerability has to actually disappear.
If the first attempt doesn't land, the agent gets a bounded number of retries with the verifier's feedback. If it still can't fix it cleanly, no PR opens and the failure is surfaced for a human.
Every PR ships with the proof: scanner output before, scanner output after, and the diff that closed the gap. When a patch attempt can't open a PR, you get a structured failure reason instead of a silent skip.
Patching removes authoring cost, not the human approval. No PR is ever auto-merged. No merged patch is ever auto-reverted. Your developers stay in the driver's seat.
Patches arrive as draft pull requests under a clearly labeled Keygraph bot. Easy to spot, easy to attribute.
No second review surface. The PR sits in your existing GitHub or GitLab queue alongside every other change.
Patching never spawns automatically. Someone clicks the finding in Keygraph. That's the trigger.
A PR opens only when every instance of the vulnerability inside its default scope is patched and verified. All-or-nothing.
Schedule a demo and watch Code Remediation turn a real vulnerability in your codebase into a draft pull request.