Keygraph parses your IaC files into a resource graph and resolves cross-references: a security group attached to an EC2 instance, an IAM role assumed by a Lambda.
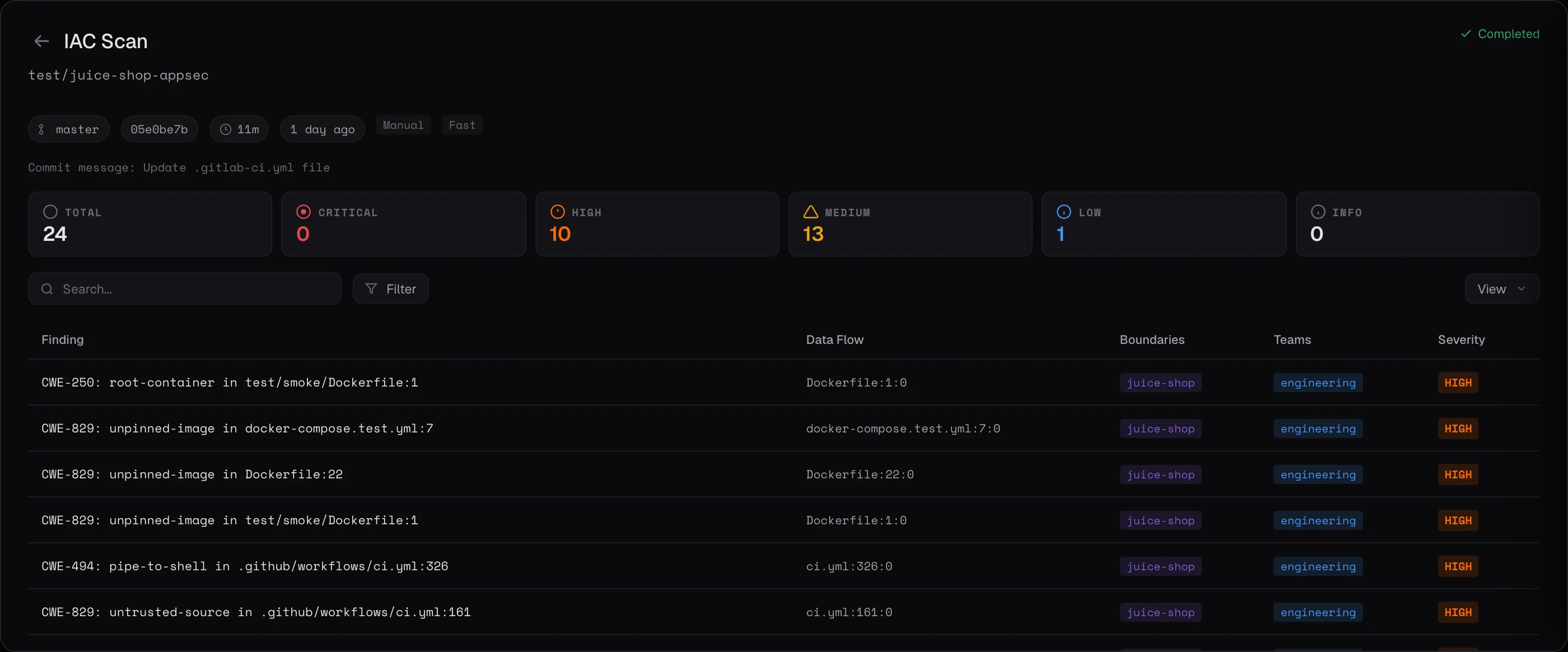
Catch infrastructure misconfigurations before they deploy. Spans Terraform, Kubernetes manifests, Dockerfiles, and CI workflows, with the context to know which findings actually matter in your stack.
Traditional IaC scanners flag rules. We flag risk. Keygraph reads your infrastructure-as-code alongside your application code, understands how resources reference each other, and evaluates whether a finding is real danger or expected behavior.
Four categories of infrastructure risk, evaluated in the context of how your resources actually connect.
S3 buckets with public ACLs, security groups open to 0.0.0.0/0, databases accepting external connections.
Wildcard permissions, overly permissive trust relationships, service accounts with admin scope.
Unencrypted storage, disabled KMS keys, missing TLS on in-transit traffic between services.
Containers running as root, hostPath mounts, privileged flags, disabled security contexts.
Every IaC finding ships with a natural-language description: what went wrong, why it matters in your stack, and how to fix it. Real-time progress tracking surfaces scan status during active runs.
Four stages, from module parse to prioritized report. Every finding is evaluated against the rest of your codebase before it reaches you.
Keygraph parses your IaC files into a resource graph and resolves cross-references: a security group attached to an EC2 instance, an IAM role assumed by a Lambda.
Every potentially-dangerous resource is checked against baseline policies (CIS, NIST 800-53) plus an LLM contextual pass that asks the question that actually matters: given this VPC topology, is this rule genuinely exposed?
Findings cross-checked against the rest of your codebase. A public S3 bucket is fine if it serves static assets, critical if a Lambda writes PII to it.
Prioritized by real-world risk, not raw CVE severity. Every finding ships with the cross-references that make it dangerous.
Keygraph emits IaC findings in standard SARIF and pushes them through the same canonical findings deduplication and dashboard as everything else. One vulnerability, one canonical entry, no matter which scanner flagged it.
Every major IaC format, with cross-resource resolution and module-level understanding.
Reads modules and tracks cross-resource references. Understands remote state, data sources, and provider aliasing.
Manifests, Helm charts, Kustomize overlays. Checks RBAC, pod security, and network policies together.
Full nested stack resolution. IAM analysis across stacks, with cross-stack output and import tracking.
Dockerfiles, compose files, base image audit. Layer-by-layer inspection with build-arg propagation.
Every scan produces an exportable report mapped to the compliance frameworks that matter. Baseline policies built in. No custom rule authoring required to get started.
See a sample report →Schedule a demo and watch IaC Scanning run against your Terraform modules and Kubernetes manifests.