Maps the codebase end-to-end: entry points, auth flows, database access, and security sinks. Static reasoning only. No browser yet.
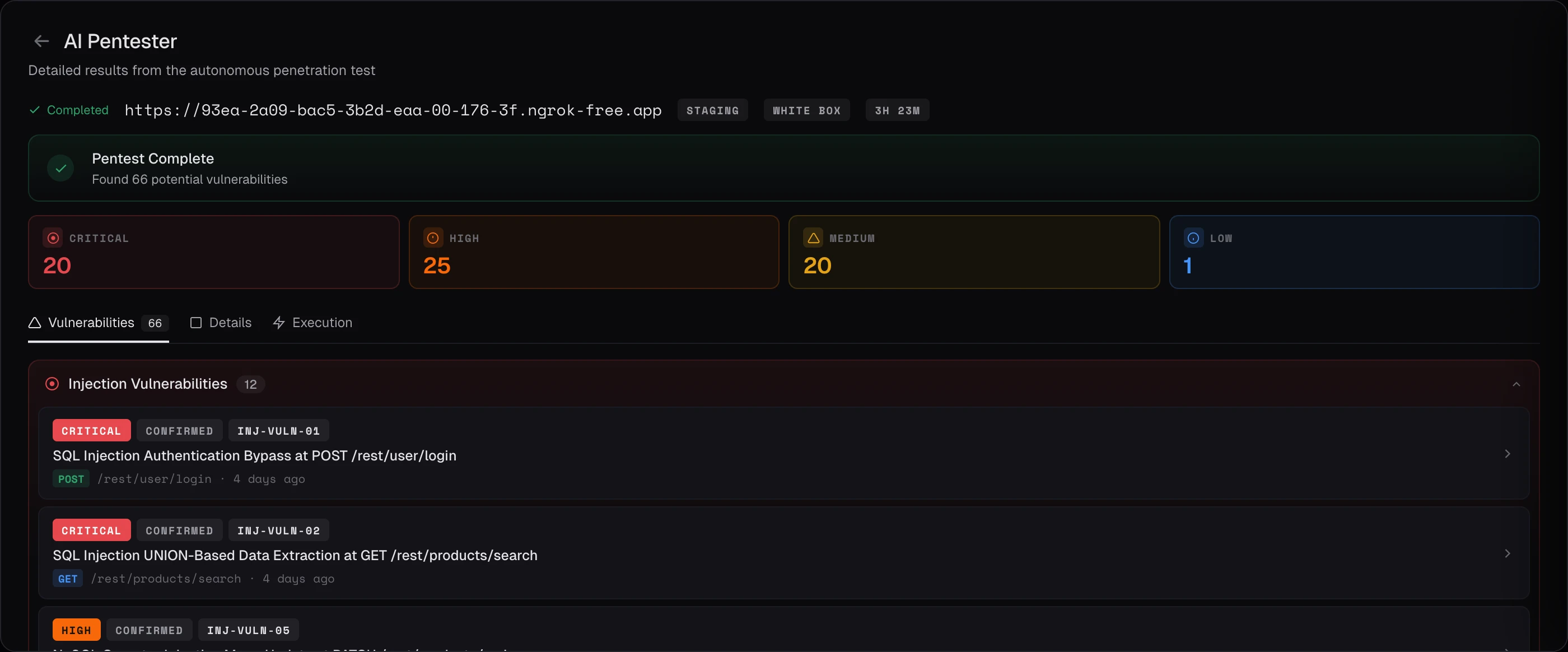
An autonomous pentester with full source-code access. Reads your code, runs the live app, and ships only what it can actually exploit.
The Whitebox Pentester doesn't pattern-match. It forms hypotheses, reasons about attack paths, and generates working proof-of-concept exploits. 13 specialized agents across 5 phases: phases 1, 2, and 5 run sequentially, phases 3 and 4 run pipelined and parallel.
Maps the codebase end-to-end: entry points, auth flows, database access, and security sinks. Static reasoning only. No browser yet.
Crawls the live app to confirm endpoints, forms, and auth boundaries. Adds Nmap and Subfinder for infrastructure scope.
Injection, XSS, Auth, SSRF, and Authz specialists each build an exploitation queue for their domain.
Each analyst hands off to a paired exploiter that crafts payloads, runs them live, and confirms working PoCs. Skipped if the queue is empty.
Synthesizes verified exploits into the final report. Speculative findings are dropped. Only confirmed evidence ships.
Each domain is covered by a dedicated agent pair: one analyzer that combines static and dynamic signals, and one exploiter that fires real attacks. Because the agents run in parallel, the pipeline moves at the speed of the slowest domain, not the sum.
Traces user input from source to dangerous sink using the code graph, then fires structured payloads against each confirmed vector.
Finds sanitization gaps and context-escape bugs in render paths, then validates with real browser payloads executed via Playwright.
Identifies server-side fetchers and URL parsers in code, then probes cloud metadata APIs, internal endpoints, and private services.
Reads session, token, and login logic directly from source, then tests bypass paths, fixation, and credential edge cases at runtime.
Maps object-ownership and role checks across controllers, then attempts horizontal and vertical access as real authenticated users.
Existing SAST results are the pentester's starting line. Every static finding is enriched, mapped, queued for exploitation, and linked back to its origin in the canonical findings table. The static findings that survive become the ones worth fixing.
Pulls the latest SAST SARIF, parses file paths, line numbers, and CWE categories into a structured queue, and tags each finding with priority, confidence, and application context.
Maps each CWE to an OWASP Top 10 category. Only secrets, data-flow findings, and point issues that land in an in-scope OWASP category enter the exploitation queue.
Injection, XSS, SSRF, Auth, and Authz agents each pull from their queue and attempt working proof-of-concept attacks against the live application, focused on locations the static scanner already flagged.
Cross-scanner deduplication links the dynamic exploit back to the original SAST finding via canonical ID, content hash, or LLM semantic comparison. A SAST entry in auth.go:142 and an exploit against POST /login become the same canonical finding.
A noisy static scanner becomes a calibrated one. The static findings that survive the pentester are the ones worth fixing.
Findings are deduplicated through a two-path system: a content hash for identical exploits, and an LLM semantic comparison for cases where different payloads target the same underlying root cause. The system is intentionally conservative: when in doubt, it reports rather than suppresses.
Deterministic match for identical exploits. If two findings hash to the same value, they collapse into one canonical record.
An LLM recognizes when different payloads target the same underlying root cause, so variant exploits collapse without losing distinct vulnerabilities.
Conservative-by-default behavior: when the deduplicator is uncertain, it surfaces both findings rather than silently merging them. You get fewer dashboards full of duplicates and zero quietly suppressed bugs.
Watch the pipeline run end-to-end against a real codebase, on a call with our engineering team. Self-hosted, in your VPC, with your own LLM keys.