01
Discovery
Discovery Agent
Reads your code end-to-end and defines business invariants: security-critical rules unique to your application, such as multi-tenant data isolation, checkout totals that must never go negative, role-based access boundaries, rate-limiting enforcement, and state machine transitions that shouldn't be skippable.
02
Violations
Violation Search
Systematically walks the codebase looking for places where each invariant breaks. Missing authorization checks on admin endpoints, tenant ID filters that can be bypassed via parameter tampering, payment flows where amount validation happens client-side only.
03
Confirm
Confirm Violations
Each candidate violation is confirmed against the actual code to rule out false positives.
04
Every confirmed finding gets a full proof-of-concept exploit with step-by-step reproduction instructions: the exact HTTP requests, parameter values, and sequencing needed to demonstrate the vulnerability in a running environment.
SARIF-compliant output
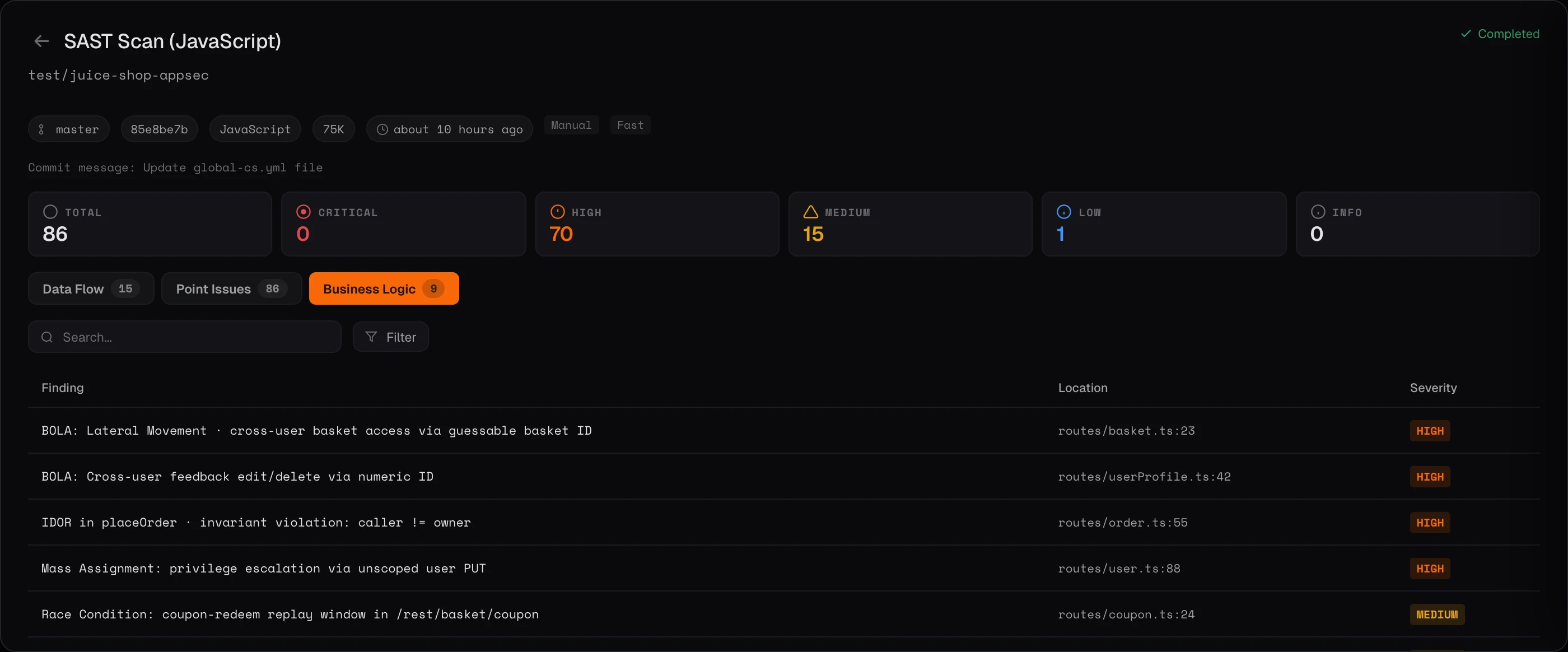
Unified with SAST, secrets, and SCA in one dashboard.
Because Business Logic Testing runs inside the SAST pipeline and emits findings in standard SARIF, results merge with other SAST findings and flow through the canonical findings deduplication system.