Images pulled from Docker Hub as OCI archives using skopeo, without requiring a running Docker daemon. Credentials encrypted and decrypted only in the main orchestration worker.
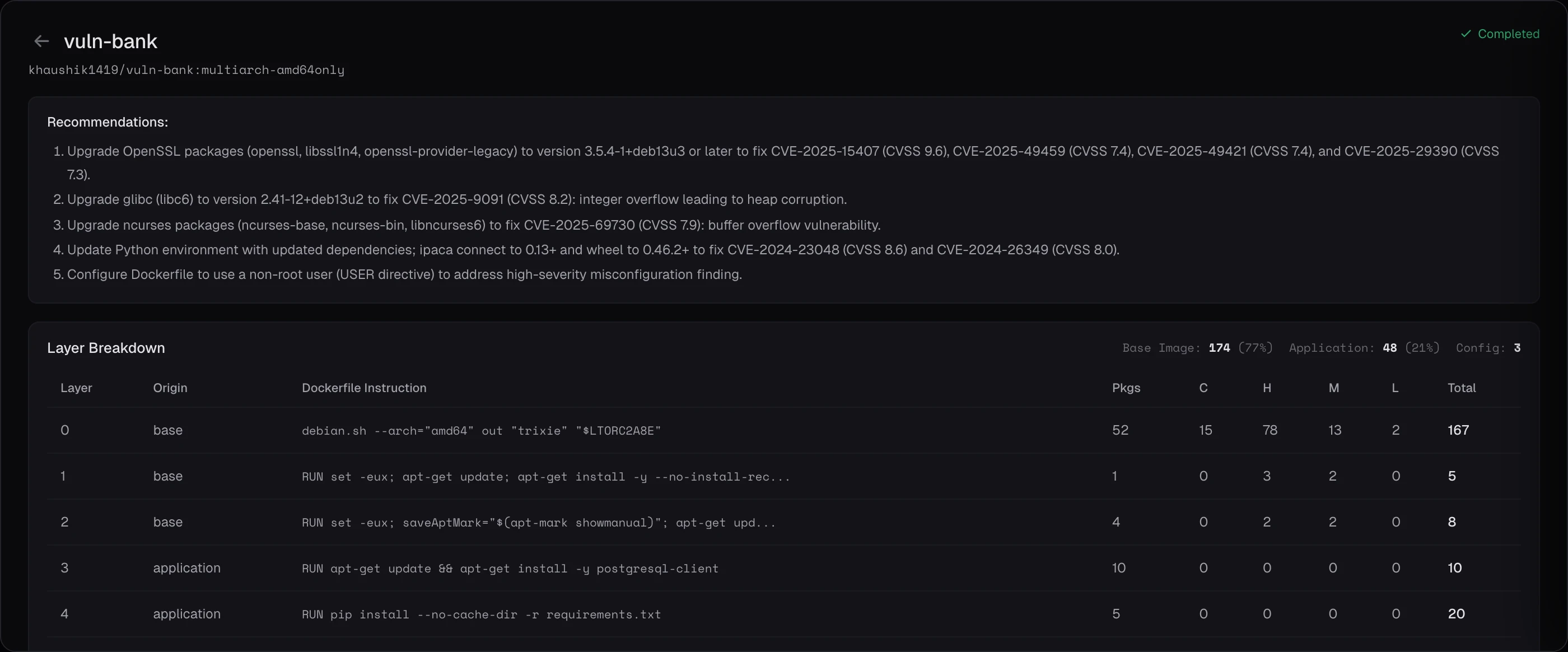
Deep vulnerability analysis across every layer of your Docker images. OS CVEs, hardcoded secrets, and container misconfigurations, surfaced before they reach production.
Every layer. Every file. Every secret ever committed. Keygraph pulls images as OCI tarballs into isolated, ephemeral compute. Three specialized tools scan every file across every layer. SBOMs ship automatically.
Specialized scanners running in parallel against every image. CVEs in OS packages, secrets across all layers, and misconfigurations in image build settings.
Scans OS packages (deb, apk, rpm) against NVD and vendor advisories. Layer-aware findings attribute vulnerabilities to base vs. application layers.
Detects 150+ secret patterns across every file in every image layer, including ENV variables set in Dockerfiles.
CIS Docker Benchmark checks: running as root, missing HEALTHCHECK, latest tags, ADD vs COPY usage, exposed ports, and more.
Four stages from registry to a unified finding: pull the image (no Docker daemon needed), scan every layer, generate the SBOM, and merge results into the rest of your security data.
Images pulled from Docker Hub as OCI archives using skopeo, without requiring a running Docker daemon. Credentials encrypted and decrypted only in the main orchestration worker.
Three specialized Trivy scanners run against each image for CVEs, secrets, and misconfigurations.
Syft generates CycloneDX and SPDX SBOMs for every scanned image, uploaded to S3 for supply chain compliance.
Container findings flow into the canonical findings table, deduplicated alongside SAST, Secrets, and SCA findings.
No daemon required. Layer-aware secret detection with full forensic coverage. Automated SBOMs. Isolated, ephemeral compute per scan.
Tarball-based image analysis using skopeo. Runs in any serverless or Kubernetes CI/CD environment.
Detects secrets committed in any layer, even if later overwritten. Full forensic coverage.
CycloneDX and SPDX SBOMs produced automatically. Compliance-ready artifacts from day one.
Scans run in ephemeral ECS Fargate tasks with organizational isolation. No cross-tenant data access.
New CVEs are picked up automatically. No manual updates, no stale scan results. Private Docker Hub repositories are supported with encrypted PAT authentication.
Schedule a demo and watch Container Scanning run against your Docker images.