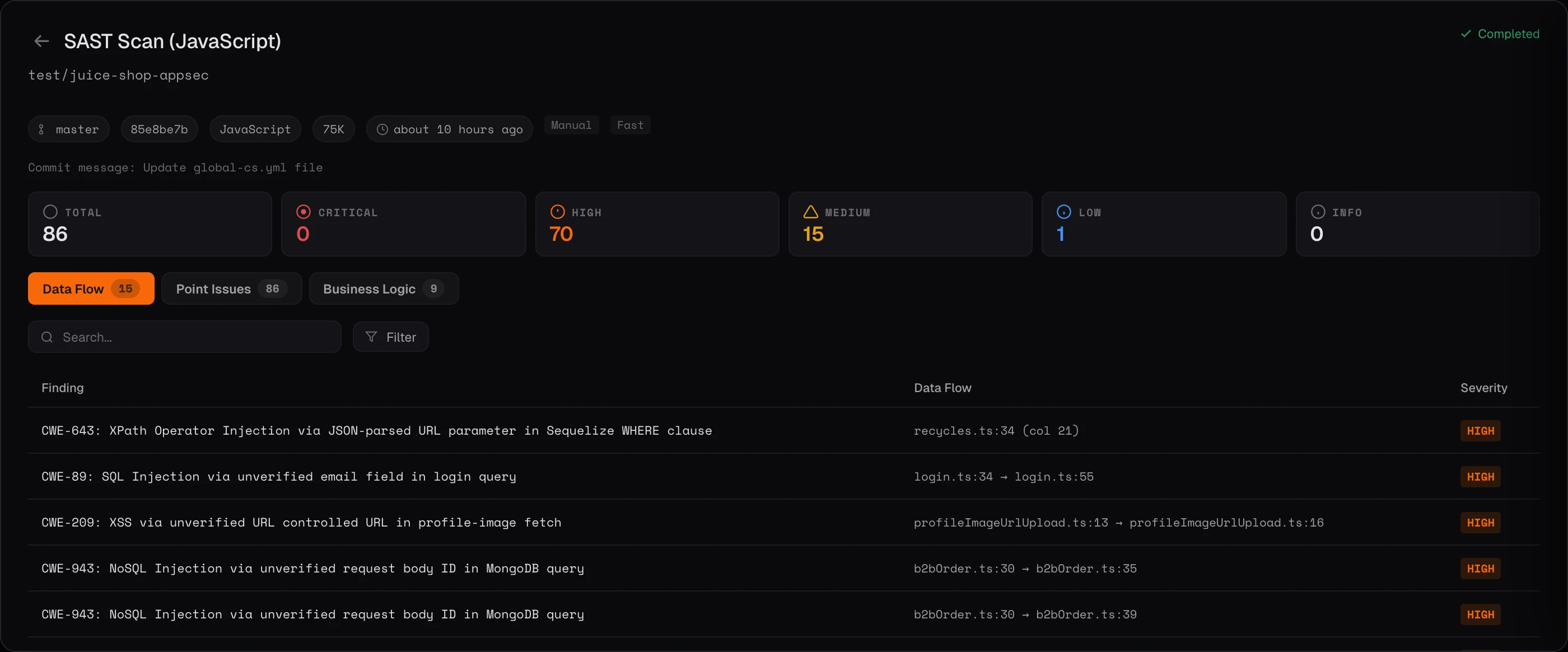
Sources (user inputs, API parameters, file reads, environment variables) and sinks (SQL queries, shell commands, file writes, response outputs) are extracted using deterministic patterns plus AI-discovered custom input handlers unique to your framework.